BleepingComputer.com.
"Why theft replaces encryption: Blue Report 2025 on ransomware and infostealers."
Views expressed in this cybersecurity, cyber crime update are those of the reporters and correspondents. Accessed on 14 August 2025, 1437 UTC.
Content and Source: "BleepingComputer.com."
URL-- https://www.bleepingcomputer.com/
Please check URL or scroll down to read your selections. Thanks for joining us today.
Russ Roberts (https://www.hawaiicybersecurityjournal.net).
Latest Articles-
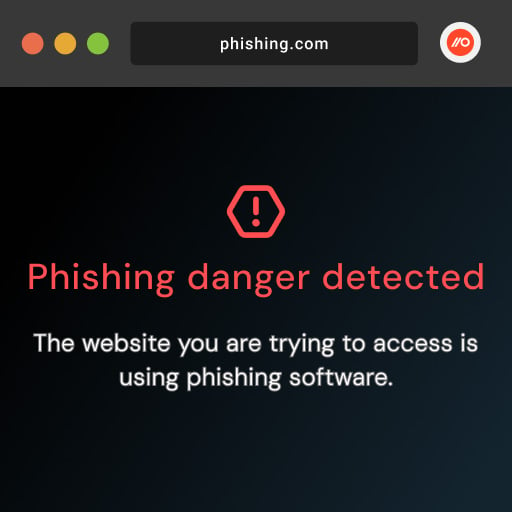
Booking.com phishing campaign uses sneaky 'ん' character to trick you
Threat actors are leveraging a Unicode character to make phishing links appear like legitimate Booking.com links in a new campaign distributing malware. The attack makes use of the Japanese hiragana character, ん, which can, on some systems, appear as a forward slash and make a phishing URL appear realistic to a person at first.
- August 14, 2025
- 10:23 AM
 0
0
-
Threat actors are leveraging a Unicode character to make phishing links appear like legitimate Booking.com links in a new campaign distributing malware. The attack makes use of the Japanese hiragana character, ん, which can, on some systems, appear as a forward slash and make a phishing URL appear realistic to a person at first.
- August 14, 2025
- 10:23 AM
 0
0
When Theft Replaces Encryption: Blue Report 2025 on Ransomware & Infostealers
Ransomware and infostealers are winning on stealth, not encryption. Picus Blue Report 2025 reveals just 3% of data exfiltration attempts are stopped. Find and fix your biggest exposure gaps before they're exploited.
- August 14, 2025
- 10:01 AM
 0
0
-
Ransomware and infostealers are winning on stealth, not encryption. Picus Blue Report 2025 reveals just 3% of data exfiltration attempts are stopped. Find and fix your biggest exposure gaps before they're exploited.
- August 14, 2025
- 10:01 AM
 0
0
New Whitepaper: The Evolution of Phishing Attacks 
Modern phishing has changed a lot in the past decade or so. The most sophisticated attacks — the ones that usually hit the headlines in the form of major breaches — come with a host of anti-analysis and obfuscation techniques making them increasingly difficult to detect.
Get the whitepaper to learn about modern phishing detection evasion techniques and how to counteract them.
-
Modern phishing has changed a lot in the past decade or so. The most sophisticated attacks — the ones that usually hit the headlines in the form of major breaches — come with a host of anti-analysis and obfuscation techniques making them increasingly difficult to detect.
Get the whitepaper to learn about modern phishing detection evasion techniques and how to counteract them.
Canada’s House of Commons investigating data breach after cyberattack
These $50 open-box Onn tablets are a great deal for work on the go
If you just need a basic tablet to handle the everyday stuff, like streaming, emails, light browsing, and the occasional video call, there's no reason to overspend. The onn. 10.1″ Tablet is a simple, reliable option for people who want functionalityIf you just need a basic tablet to handle the everyday stuff, like streaming, emails,
- August 14, 2025
- 07:08 AM
 0
0
-
If you just need a basic tablet to handle the everyday stuff, like streaming, emails, light browsing, and the occasional video call, there's no reason to overspend. The onn. 10.1″ Tablet is a simple, reliable option for people who want functionalityIf you just need a basic tablet to handle the everyday stuff, like streaming, emails,
- August 14, 2025
- 07:08 AM
 0
0
Leak: OpenAI's browser will use ChatGPT Agent to control the browser
CISA warns of N-able N-central flaws exploited in zero-day attacks
Microsoft fixes Windows 11 24H2 updates failing with 0x80240069 error
Microsoft has resolved a known issue preventing the August 2025 Windows 11 24H2 cumulative update from being delivered via Windows Server Update Services (WSUS).
- August 14, 2025
- 03:41 AM
 0
0
-
Microsoft has resolved a known issue preventing the August 2025 Windows 11 24H2 cumulative update from being delivered via Windows Server Update Services (WSUS).
- August 14, 2025
- 03:41 AM
 0
0
Google Gemini's Deep Research is finally coming to API
Google Gemini's one of the most powerful features is Deep Research, but up until now, it has been strictly limited to the Gemini interface. This could change soon.
- August 13, 2025
- 09:01 PM
 0
0
-
Google Gemini's one of the most powerful features is Deep Research, but up until now, it has been strictly limited to the Gemini interface. This could change soon.
- August 13, 2025
- 09:01 PM
 0
0
OpenAI relaxes GPT-5 rate limit, promises to improve the personality
Fortinet warns of FortiSIEM pre-auth RCE flaw with exploit in the wild
Windows 11 24H2 updates failing again with 0x80240069 errors
New downgrade attack can bypass FIDO auth in Microsoft Entra ID
Deal: Get FutureMoney Pro for $100 and a $100 bonus to invest
With a FutureMoney Pro Lifetime Subscription, parents get a powerful tool to invest in their kids' dreams and get rewarded for it. When you sign up and make a qualifying contribution, you'll receive a $100 bonus investment to jumpstart your journey, making the lifetime subscription free.
- August 13, 2025
- 02:08 PM
 0
0
-
With a FutureMoney Pro Lifetime Subscription, parents get a powerful tool to invest in their kids' dreams and get rewarded for it. When you sign up and make a qualifying contribution, you'll receive a $100 bonus investment to jumpstart your journey, making the lifetime subscription free.
- August 13, 2025
- 02:08 PM
 0
0
Spike in Fortinet VPN brute-force attacks raises zero-day concerns
A massive spike in brute-force attacks targeted Fortinet SSL VPNs earlier this month, followed by a switch to FortiManager, marked a deliberate shift in targeting that has historically preceded new vulnerability disclosures.
- August 13, 2025
- 12:42 PM
 0
0
-
A massive spike in brute-force attacks targeted Fortinet SSL VPNs earlier this month, followed by a switch to FortiManager, marked a deliberate shift in targeting that has historically preceded new vulnerability disclosures.
- August 13, 2025
- 12:42 PM
 0
0
Pennsylvania attorney general's email, site down after cyberattack
Microsoft removes PowerShell 2.0 from Windows 11, Windows Server
Microsoft asks users to ignore certificate enrollment errors
Microsoft has asked customers this week to disregard incorrect CertificateServicesClient (CertEnroll) errors that appear after installing the July 2025 preview update and subsequent Windows 11 24H2 updates.
- August 13, 2025
- 08:24 AM
 0
0
-
Microsoft has asked customers this week to disregard incorrect CertificateServicesClient (CertEnroll) errors that appear after installing the July 2025 preview update and subsequent Windows 11 24H2 updates.
- August 13, 2025
- 08:24 AM
 0
0
OpenAI adds new GPT-5 models, restores o3, o4-mini and it's a mess all over again
Save $329 on this refurbished iPhone 15 Pro Max deal
One of Apple's most advanced iPhones yet just got a whole lot more affordable — and no, this isn't a back-in-stock fluke or one-day-only coupon scramble. Right now, you can score a Grade A refurbished iPhone 15 Pro Max (256GB, unlocked) for $769.99 — that's $329 off its original retail price.
- August 13, 2025
- 07:08 AM
 0
0
-
One of Apple's most advanced iPhones yet just got a whole lot more affordable — and no, this isn't a back-in-stock fluke or one-day-only coupon scramble. Right now, you can score a Grade A refurbished iPhone 15 Pro Max (256GB, unlocked) for $769.99 — that's $329 off its original retail price.
- August 13, 2025
- 07:08 AM
 0
0
Claude gets 1M tokens support via API to take on Gemini 2.5 Pro
Claude Sonnet 4 has been upgraded, and it can now remember up to 1 million tokens of context, but only when it's used via API. This could change in the future.
- August 12, 2025
- 06:13 PM
 0
0
View More
Claude Sonnet 4 has been upgraded, and it can now remember up to 1 million tokens of context, but only when it's used via API. This could change in the future.
- August 12, 2025
- 06:13 PM
 0
0





















Comments
Post a Comment
Please leave a comment about our recent post.